Network administration demands precision, efficiency, and the right tools to keep infrastructure running smoothly. Whether you're troubleshooting connectivity issues, monitoring network performance, or managing IP configurations, having reliable network tools in your arsenal is essential. In this guide, we'll explore five indispensable network tools that every system administrator should master.
1. Wireshark – The Network Protocol Analyzer
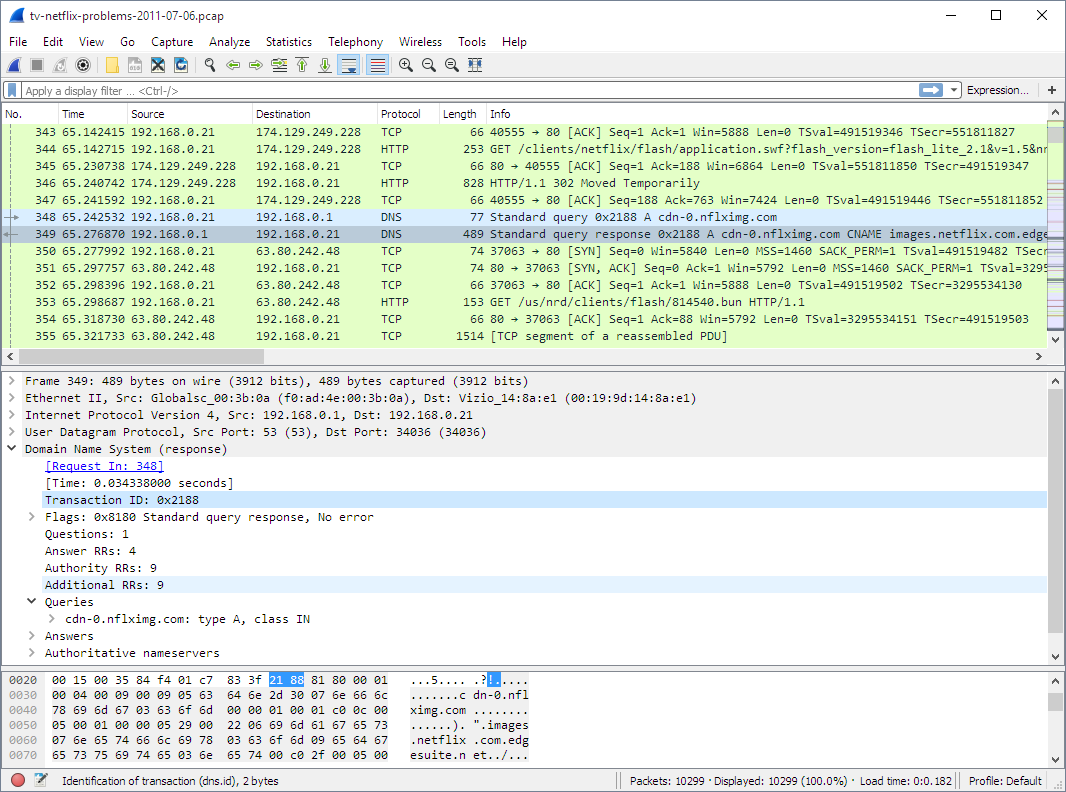
Wireshark stands as the gold standard for network packet analysis and remains an essential tool for administrators at all skill levels. This open-source packet analyzer allows you to capture and interactively browse network traffic in real-time, making it invaluable for troubleshooting complex network issues.
Pro Tip: Start with capture filters to reduce the volume of data collected, then use display filters to drill down into specific protocols or conversations. This approach keeps your analysis manageable even on busy networks.
2. Nmap – Network Mapping and Security Scanner
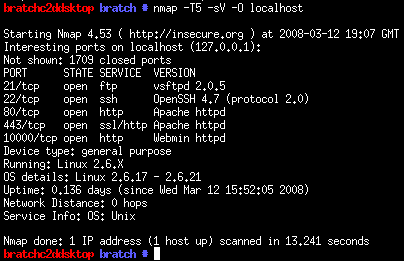
Nmap (Network Mapper) is a powerful open-source tool designed for network discovery and security auditing. System administrators rely on Nmap to inventory network devices, monitor service uptime, and identify potential security vulnerabilities before malicious actors can exploit them.
Best Use Cases: Use Nmap when conducting network audits, verifying firewall rules, discovering unauthorized devices, or maintaining an accurate inventory of network assets.
3. PuTTY / OpenSSH – Secure Remote Access
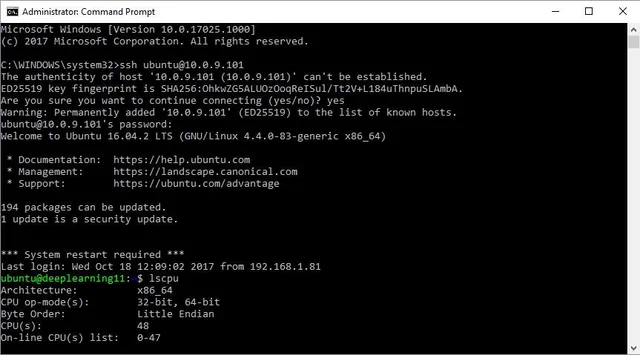
Remote access is fundamental to modern network administration, and SSH (Secure Shell) clients are the backbone of secure remote management. PuTTY remains the go-to choice for Windows administrators, while OpenSSH is standard on Linux and macOS systems.
Key Features: Encrypted terminal sessions, support for SSH/Telnet, session management, and port forwarding capabilities.
4. SolarWinds Network Performance Monitor
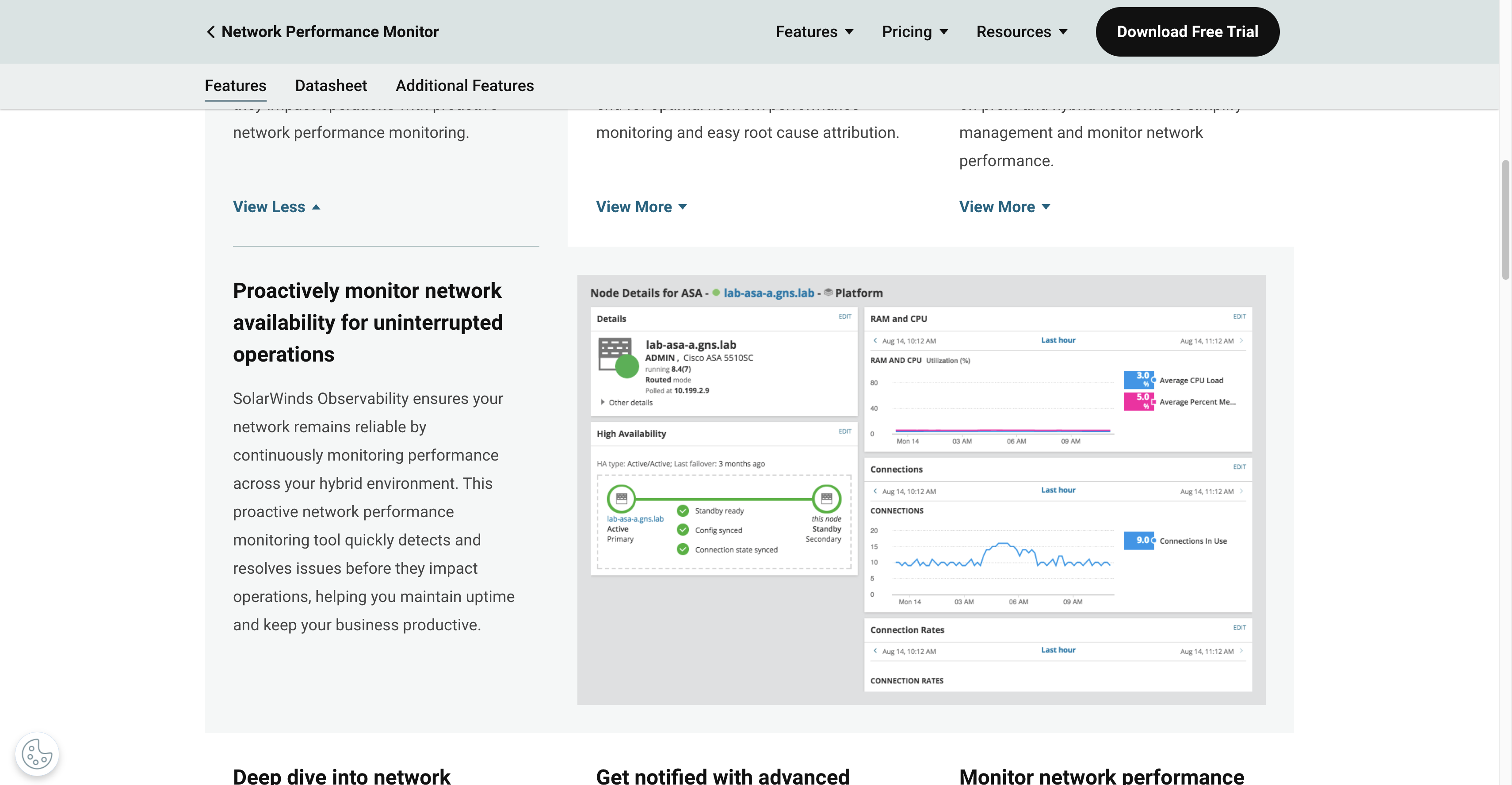
For organizations requiring comprehensive network monitoring, SolarWinds Network Performance Monitor (NPM) provides enterprise-grade visibility into network health and performance. While it's a commercial solution, its capabilities justify the investment for medium to large networks.
Alternative Options: For budget-conscious admins or smaller networks, consider open-source alternatives like Zabbix, Nagios, or PRTG Network Monitor's free tier.
5. IP Address Management Tools (IPAM)
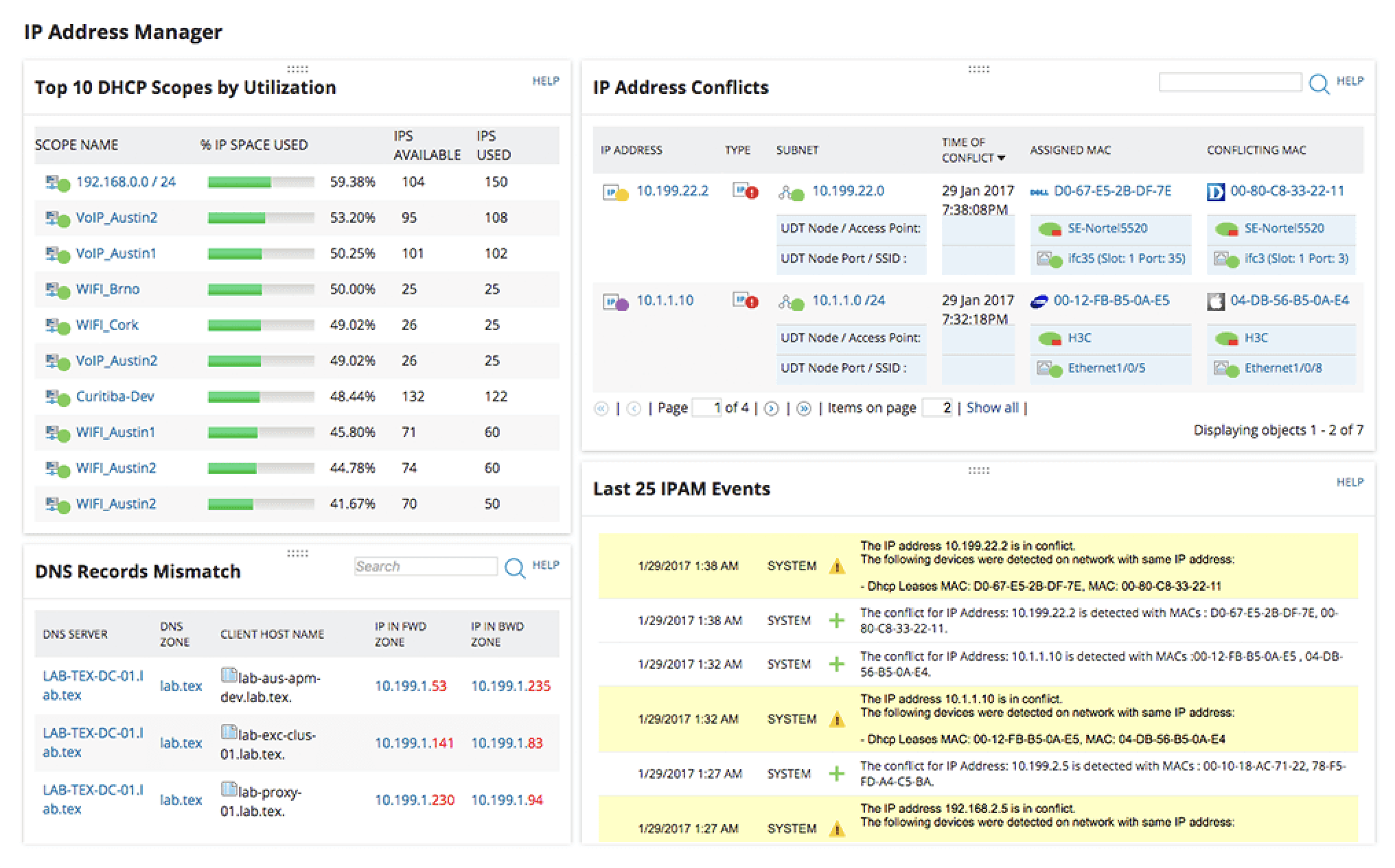
Effective IP address management is critical as networks grow in complexity. Modern IPAM tools combine DHCP, DNS, and IP address tracking to prevent conflicts and streamline network planning.
Pro Tip: Visit IP Tools Pro for free online IP tools including subnet calculators, IP geolocation, and ping utilities that complement your IPAM solution without requiring software installation.